Prof. Ben Israel said these things at a meeting where the hacking into Sony computers and the theft of the sensitive information from them was discussed, which was held by the Yuval Ne'man workshop for science, technology and security and the Blavatnik Multidisciplinary Center for Cyber Research at Tel Aviv University
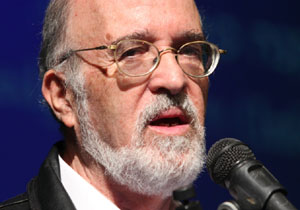
The combined terrorist incident in France illustrated how difficult it is for a Western government to deal with the threat of Islamic terrorism without harming other Muslims and the individual freedom of all citizens. The situation is similar in cyber as well - until there is an attack, the countries hesitate to invest resources in dealing with the threat. Says Prof. Yitzhak Ben Israel, head of the Blavatnik Multidisciplinary Center for Cyber Research at Tel Aviv University and Yuval Na'im Workshop for Science, Technology and Security at a joint meeting of the two centers that analyzed the hacking of Sony computers from different angles.
Israel was one of the first countries in the world, a decade and a half ago, to begin protecting its critical computing infrastructure and government websites. Israel was also the first country in the world to establish a body in the Prime Minister's Office - the National Cyber Headquarters - to coordinate and direct all members of the cyber orchestra in the country.
The government will soon make a decision centered on the question of how to protect the citizens of the country and their privacy without infringing on the privacy and rights of the citizens. Should the protection of civil cyberspace be entrusted to the security service, and risk what happened to the NSA in the US, or should the right to privacy be preferred? Is there a way to balance the needs of national security and the basic rights of every person in a democratic regime? The proposed resolution that will soon be submitted to the government deals with the establishment of an operative body - a civilian national authority for cyber defense - that will balance the two requirements above.
That authority will have to deal with increasing threats in which the border between the state and a private company is blurred. Apparently private companies should protect their information but what happens if a country attacks a company like in the case of Sony?
Ilan Greitzer, Matan Sharaf and Anbar Raz - members of the "Red Team" who voluntarily conduct audit operations that include attempts to penetrate bodies that fall between the thrones - of national importance but are not supervised by the Prime Minister or other authorities. The three described how they easily managed to break into the computer of a large hospital.
Ilan: For the past two years, we have been hearing about the collapse of large and secure organizations that are in the best of standards: Target, Lockheed Martin, JP Morgan, RSA (which, as we know, are developing the North through which, for example, payments are made on the Internet and of course the last example - Sony. If such organizations fall, what Say the small company does not have the same resources and capabilities.
But you don't need a sophisticated cipher to get into the computers of employees at these institutions, and there are enough former employees who still have privileges. Entities like hospitals don't even know how many computers they have, how many of them are connected to external networks, and whether people are allowed to enter the building of the computer center. "If the answer to one of the questions is yes, the hackers have won."
Inbar Raz listed a series of malfunctions arising from the human interface - for example, reusing the same passwords for social networks, shopping at banks, etc. Not all of these sites are secure and there are even those whose list of users and passwords is not encrypted. Today, the situation has even worsened because all these services can be accessed through Facebook.
An interesting way of hacking is by connecting the computers and phones in the organization to a system that records and broadcasts their content - they built a charger for cell phones that has everything needed to charge a phone but also electronic components used for listening. When someone charges their iPad or iPhone, the system drinks all of its contents. Looking at the computer socket on the wall of the conference room, Raz said that all the university's computers can be accessed from there, even the salary computers.
Matan: We need one point to enter through. The defender has to be able to defend all the time, and it is enough for the attacker to be successful once.
Eran Ziv, CEO of Security Dump, allowed Sony to distribute the film "The Interview" because of which government officials allegedly hacked into Sony's computers. This was concerned that once the films were released, there would be a denial of service attack on the servers where they are kept, and the Israeli company provided them with support for Redware's denial of service attack prevention system. "In this case it is a complex project because the film is stored on hundreds of servers around the world. We routed all requests to download the movie through us to detect a denial of service attack before it reaches Sony's servers, but luckily there was no such attack."
Andrey Dolkin - the director of cyber attack research at the CyberArk company says that the weak point is the privileged accounts of administrators, and this was also the case with Sony. One morning the employees came to work, opened their computers and there was a message on it that they had been attacked. After that, files were deleted for those who did not close the computer in time. Before they were deleted, they were copied to the hackers' computers and thus five films were published before they were released, which caused direct damage to Sony. Word and Excel files that contained passwords and even a text file called accounts without a password were also stolen.
Among other things, sensitive e-mail files of senior executives including the CEO were also exposed, which included details of the stars' salaries, scans of employees' passports and medical information. It is not clear how Sony will deal with the workers' claims.
Dulkin quoted the CEO of the Mendiant company, which provides an immediate period service, according to which this was a sophisticated attack that cannot be prepared for.
The intrusion was carried out using a worm that spread in the company's internal network using the SMB protocol and analyzes password contexts while searching for the administrative passwords. There was a similar attack in early 2014 on the servers of the Sands company's casinos, following the statement of its owner - Sheldon Adelson that Obama should bomb Iran's nuclear facilities. The Iranians penetrated a test server, and as soon as an administrator entered it, they captured the password and penetrated through it to the active servers.
His research at CyberArk is about a way to disconnect his personal threshold and password from the automatically managed corporate infrastructures.
Mani Barzilai, a colleague at the Yuval Na'am workshop and a member of the senior forum, emphasized the fact that there is a blur between the security sector and the civilian sector. Civil societies are under attack or helping governments defend against attacks.
There is no answer to the question of where the responsibility of the state begins and where of society. Obviously, the bank has guards who are supposed to deal with local threats, a country can protect a country. The state has exclusive authority to attack if we do proactive security this is actually an attack.
Amit Ashkenazi from the National Cyber Headquarters presented the legal position. "The state and legal handling of events of this type should be based on the level of the organization and the level of the state. What is required at the organization level to be better organized. Until today, the perception was that preparing for cyber incidents are part of the organization's internal risk management and that the government only has a role in essential organizations and in the management of databases.
The perception of the headquarters is that in order to reduce the cyber risk, it is necessary to step up the role of the state. The organizations are expected to do the things that the government asks of them in order to be prepared. Another question is whether market forces are efficient. In the field of personnel, services and products there are information gaps, even if an organization wants to invest the remaining shekel in this, it is not sure that it will be effective. The government has a role for the shekel to be effective.
One of the legal derivatives is the need to define the information security professions. In the US they say that the lack of uniform terminology in the security professions harms national security.
The government also controls the sectoral regulation. Sectoral regulators such as the supervisor of banks and the commissioner of the capital market.
An equally important legal issue is what is the role of the state in events of this type. We extend the information security problems of the organizations into cyberspace. There is no black and white here. Like terrorism, the terrorist organization is at the forefront. You need a person who will learn the system and understand it in routine and certainly in an emergency. The IT manager must be prepared for this emergency
The role of the state is to engage in solving the gap in information sharing. In Western countries it is implemented by establishing a national CETRT. The fear is that the state's entry into the supervision of the Internet could result in a violation of privacy rights and freedom of information. All these are also joined by the metadata - the systems constantly record what the surfers do. Companies like Kaspersky, McAfee and Microsoft have a better picture of what is happening in Israeli cyber than the government.
In conclusion - the legal strategy of the headquarters, as part of the overall strategy of the information, is to strengthen the organizations in dealing with routines and where we think that the organizations see too much the chance and not the risk to indicate the risk, to remove legal barriers within the organization (employees, customers) and monitor.
Dov Hausen Kuriel, the company of the Multidisciplinary Cyber Center presented the issue of the three class action lawsuits by the Sony employees who left in the meantime against the company.
The lawsuit stems from the fact that even though Sony knew about the attack for weeks, they did nothing to stop the leak of the sensitive information. "This claim has a solid basis. Sony did not take care of sufficient protection - Excel tables are not protected, the company also ignored a professional opinion of the security personnel. The company did not update the employees for a week, did not publish the extent of the damages, did not share the steps being taken. Nor were lessons learned from the 2011 Sony PlayStation hack (a separate sister company).
The grounds for the lawsuit - failure to report a hack as required by Hitken in 47 of the US states, failure to fulfill the obligation to protect computers, servers, storage of personal information, i.e. negligence. Violation of the right to privacy at the constitutional level. There are also requirements for the protection of certain types of information such as medical and financial information.
So far we have not seen Sony shareholders who filed a personal lawsuit, it should be noted that derivative lawsuits can be filed against the company's managers.
In conclusion, Hausen-Khoriel says: "I am interested to understand that the legal battle at such a level of representative insight from Sony is completely disconnected from the identity of the attacker. From a dry legal point of view, the attack, the defenses and the treatment is something that happens independently of the question of who is the attacker and of all the historical and diplomatic background to the event."
Ram Levy (complete from his slides) described the insurance aspect of a cyber attack.
"Sony's method of attack is not new. It was used in the Aramco attack in 2012 and in the attack in South Korea. Attacks on Sony are not new either, in 2011 the Sony Playstation company was attacked, which operated an insurance policy, was liquidated but had to change company to AIG. According to what was ironically revealed in the documents published by the attackers, the amount of the premium was between 80 and 100 million dollars.
AIG can dismiss the claim on the grounds of negligence because it ignored North Korea's threats. Such a policy is a type of terrorism policy, in which the person who determines the indemnity is the underwriter and not an actuarial calculation, this in the absence of sufficient experience in operating such insurances.
Even if from a material point of view, 80 million dollars is not serious for the insurance companies, but what will happen if companies are damaged where the damage will be 800 million, and what if 100 of them are damaged at the same time. It is also a threat with a very large amplitude, it is impossible to even imagine what would happen if an attacker caused the disruption of the Oracle database on which the information industry is founded.
In three years the insurance market for terrorist risk cases in general and cyber in particular will change. More companies will enter the field, they also invest in the development of actuarial models. The premiums will start to decrease but the insurers will require a risk survey which costs quite a bit. The insurance companies will also oblige their customers to implement recovery solutions in exchange for a reduction in the premium.

5 תגובות
The entire population register of Israel was leaked to the network. There is illegal software! On behalf of Agron who provides this information! What do the police do if it? Enough with the panic, because a terrorist can strangle a pilot with his bare hands, a can of Coke. In the end, a terrorist is a sick/frustrated person who, with quick action, can prevent the damage, and maybe make him even save himself.
In the same way that no one wants to get on a plane whose passengers have not passed a security check, so as an inverse paraphrase, the majority of citizens will be prepared for a substantial violation of their privacy, but receive in return effective protection against cyber attacks.
In light of Bibi's shameful attitude towards Israeli Arabs. Perhaps it would be worthwhile to appoint a Druze lieutenant colonel as Minister of Defense. Internal stability is more in danger than cyber threats or Iran. Bibi sold his soul to the devil to become prime minister.
Any database will be hacked, the question is how to minimize damages. Identity theft, what is the work procedure in such a case? Let's say that a friendly country steals an Israeli identity for the purpose of spying in a third country, how do you act? Or an innocent citizen whose life has been destroyed, is there a person who can help him and the police, and give him back his identity and his life.
Or suppose there is a powerful prime minister, who is spying on his employees or his political opponent?
How will the police deal with it?