Hayadan > Computing and technology > Computing and robotics > computer technology
computer technology
- Tel Aviv University
- December 1, 2023
We all know the cliché: "Men are from Mars and women are from Manga", but are men and women also distinctly different in the way they conduct war and conflict? What does digital games have to do with this? And what does this mean regarding who is desired to head the ruling parties in Israel?
- The Voice of Science website - the Israel National Science Foundation
- November 14, 2023
An advanced algorithm makes it possible to quickly retrieve information from the memory of systems such as phones and computers and correct errors
- Tel Aviv University
- October 28, 2023
Dr. Sandrin Bodna, Head of the Department of Communication at Tel Aviv University, gives tips on how to behave on social networks and in the media against fake news
- The Voice of Science website - the Israel National Science Foundation
- October 5, 2023
The interaction between man and computer grew out of the activities of hackers in the 50s and the books and films that influenced them
- The Voice of Science website - the Israel National Science Foundation
- September 17, 2023
To attract traders, crypto exchanges artificially inflate their activity volume. does it work?
- The Voice of Science website - the Israel National Science Foundation
- August 6, 2023
A virtual environment that simulates public spaces will make it possible to discover spatial geometric principles that improve the ability to navigate, especially in the elderly
- The science service
- August 1, 2023
- No comments
The virtual twin experiences support sustainable steel production by companies seeking to optimize work processes and reduce their carbon footprint
- The Voice of Science website - the Israel National Science Foundation
- July 19, 2023
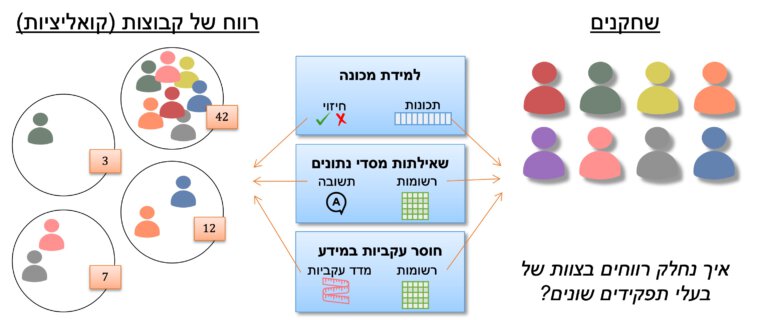
Researchers at the Technion have developed algorithms that detect errors in databases
- Avi Blizovsky
- March 30, 2023
- 3 תגובות
Engineers from the University of Arizona have developed a system that allows autonomous vehicles to scan underground habitats for astronauts
- Avi Blizovsky
- March 26, 2023
- One response
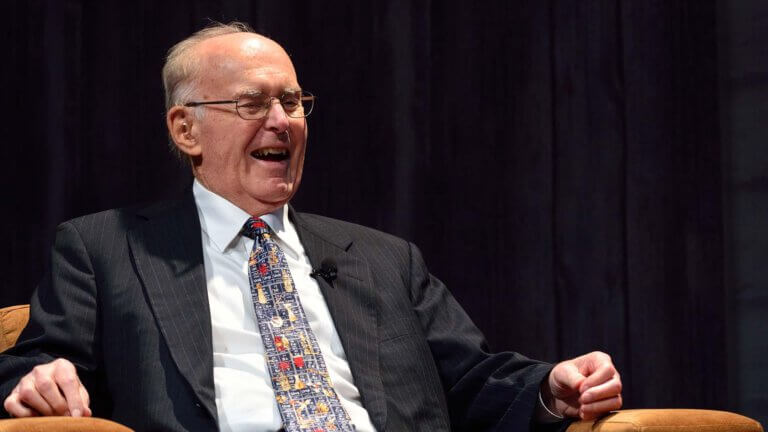
Moore became especially famous thanks to the law he coined - Moore's law describing the rate of development of chip technology which today is everywhere
- The Voice of Science website - the Israel National Science Foundation
- March 11, 2023
Researchers were able to minimize distortion created in geometric bodies due to their flattening or stretching
- Avi Blizovsky
- February 11, 2023
- One response
This is a joint study by researchers at Bar Ilan University, the Technion and the University of Calabria in Italy that dealt with EDAM type memories
- The Technion
- February 7, 2023
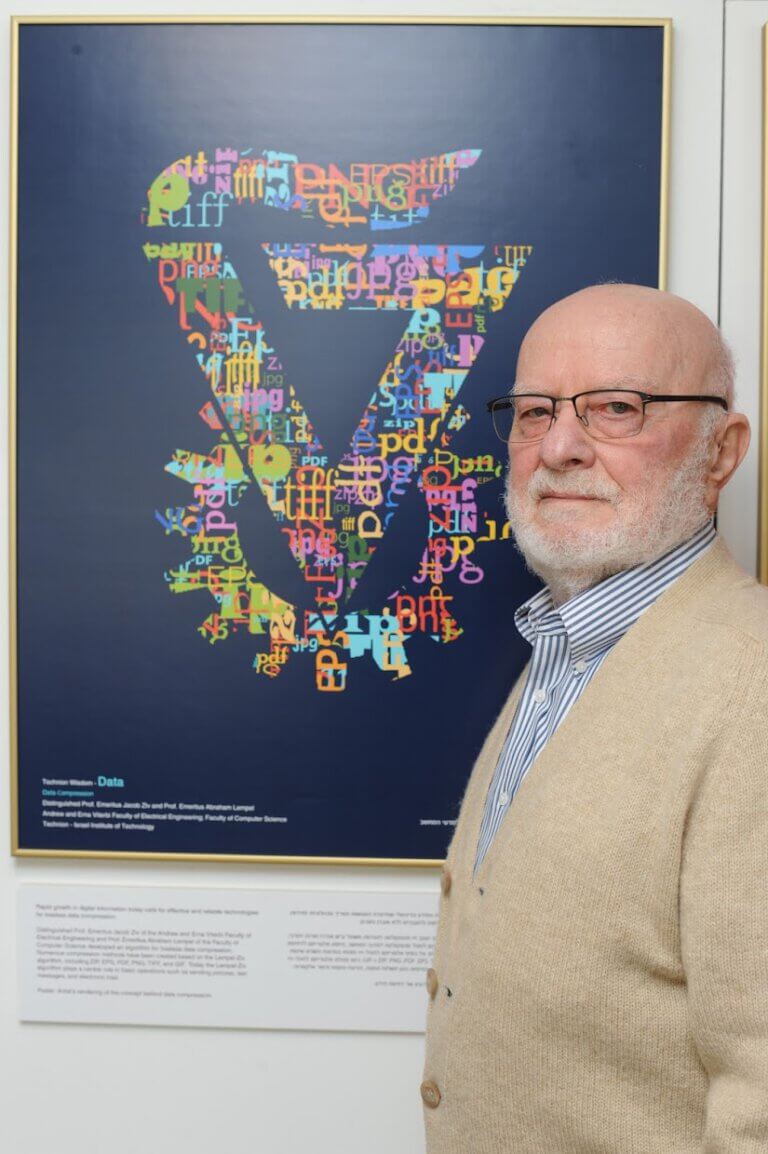
Prof. Lampel was a partner in the development of the Lampel-Ziv algorithm, an algorithm that changed the world of compression and is considered one of the most significant technological breakthroughs achieved in the State of Israel and in the history of the Technion by its researchers
- Tel Aviv University
- March 10, 2022
Ukraine was prepared not only for the physical war being waged there, but also for cyber war. This explains, among other things, the request of the Ukrainian government from Elon Musk for modems for the Starlink space internet systems
- Dr. Moshe Nahamani
- July 19, 2021
- No comments
Until now as too elusive, but researchers from Stanford University claim that they have succeeded in bringing about a breakthrough in this field
- Angle - a news agency for science and the environment
- May 5, 2021
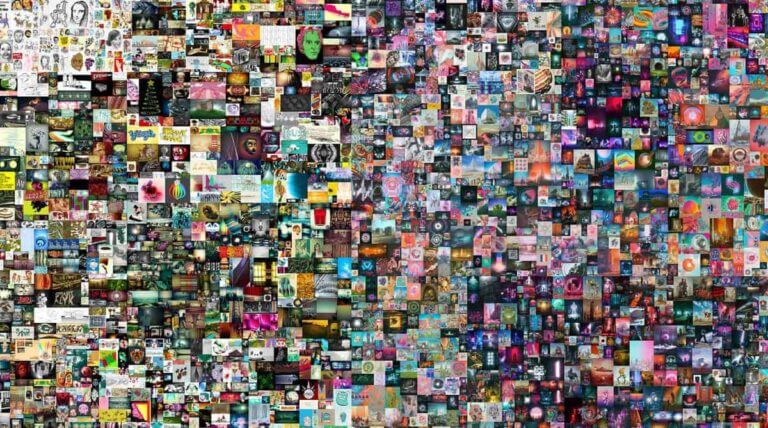
The new technology has recently allowed a new market of internet art to skyrocket, with sales in the millions of dollars, but even though none of the artworks sold as NFT are in the physical space, the "real" - their environmental costs due to the mining operation, we all pay
- Dr. Tomer Simon
- April 26, 2021
- 3 תגובות
Most likely, this article will be read on the screen of your phone, whose color and sharpness are only possible thanks to the rare metals inside it. Inside every smartphone on Earth are 16 of the 17 rare earth metals, most of which are mined in China
- Guest article
- March 23, 2021
- One response
AMLAK: Do not provide your account details or personal details and block the credit card from reuse on the site/game
- Ben-Gurion University
- October 1, 2020
- No comments
According to a new study published in the journal Computers & Security, the ability to launch cyber attacks (DDoS) through a bot network is growing at an increased rate and is a real risk to every person with a smart device and also to the providers of communication services, whose infrastructures may be compromised
- The Technion
- June 30, 2020
- 2 תגובות
- Angle - a news agency for science and the environment
- March 21, 2020
- One response
- Avi Blizovsky
- March 19, 2020
- 4 תגובות
- The science service
- July 18, 2018
- 3 תגובות
- Guest article
- June 2, 2018
- One response
- Dr. Moshe Nahamani
- April 30, 2018
- 3 תגובות

















![One of the innovative features of the XNUMXD printing method on the skin is the printer's ability to use computer vision to track and adapt to the body's movements in real time University of Minnesota] McAlpine [Courtesy: Group](https://www.hayadan.org.il/images/content3/2018/04/3d_printing_on_hand_original_648x432_0.jpg)