Historical sources, methods of operation, identification characteristics, advantages and disadvantages. And of course, the question of privacy * Big brother or gatekeeper?
By: Anil K. Jain and Sharath Pankanti
Like many others, you too must navigate your way through your day-to-day life using a variety of cards and passwords that confirm your identity. But if you lose one such card, the ATM will refuse to provide you with money. If you forget a password, your PC will refuse your commands. If your cards or passwords fall into the wrong hands, those measures that were intended for protection purposes will become tools for fraud or identity theft. The field of biometrics, which deals with the automated identification of people based on unique anatomical and behavioral characteristics, can overcome many of these problems.
Unlike physical means, such as a credit card or password, biometric characteristics are difficult to forge, copy, share, lose or guess. The use of biometric characteristics is actually the only way to determine if a certain person has been issued several official documents, such as a driver's license or passport, under different names. On top of that, using these characteristics to prove identity is relatively simple. Therefore, biometric systems are becoming more and more common in recent years. The market already has, for example, laptops and mobile phones that recognize fingerprints. In some countries, biometric security measures are used to protect ATM cards and passports, to determine whether a person has permission to enter a building, or to verify that a person is eligible for welfare payments. Although these systems are far from perfect, there is no doubt that today, when the sensors are already cheap and the microprocessors are powerful, the biometric technology will continue to spread.
The dimensions of a person
Biometrics is not a new idea. In 1879, Alphonse Bertion, a French police inspector, proposed building a complicated system of body measurements, including arm and leg lengths, to identify serial criminals. In the decade that followed, British scholars proved that each fingerprint is a unique pattern that does not change with the passage of time, thus laying the foundations for the invention of the identification method based on fingerprints in 1896. A short time later, Scotland Yard began collecting fingerprints left at crime scenes to identify criminals. Today, almost every law enforcement organization in the world relies on fingerprints to identify criminals, solve crime mysteries, and conduct background checks on people applying for sensitive positions.
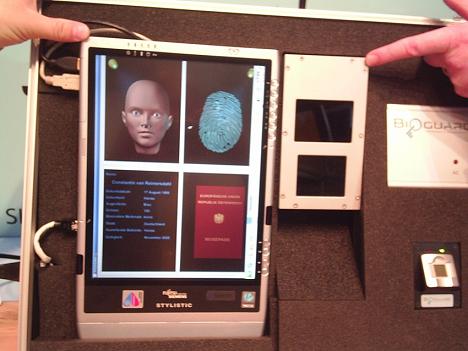
Smart identity cards - soon with you
However, fingerprints are not the preferred identification feature for all purposes. Identification systems use additional behavioral and physical characteristics, sometimes separately and sometimes in combination. Today, emphasis is placed on designing fully mechanized biometric systems, very fast, accurate, user-friendly, whose cost is relatively low relative to their usefulness, and which can be integrated into existing security infrastructures. In addition to identification systems based on fingerprints, identification systems based on face, hand, voice and iris (the colored part of the eye) characteristics have been developed in the last 30 years.
Biometric identification is based on characteristics that have two fundamental properties: they are unique to each person and do not change significantly over time. Some features allow for a high level of accuracy, while others allow for ease of use or low cost. Selecting a characteristic as an identification factor therefore depends on the objectives of the identification system. There is no single measurement that is optimal for all uses.
Let's look at the three most common features today: fingerprints, face and iris. Fingerprints are used not only for forensic purposes, but also for automatic identification systems at border crossings in several countries. In the United States alone, the VISIT-US program of the US Department of Homeland Security has processed data from more than 75 million visitors since it was put into use in 2004. Commercially, one of the biggest advantages of using fingerprints is the low price of the sensors (about five dollars) and their small physical size. This allows them to be integrated into consumer products, such as laptops and mobile phones and even flash memory cards. However, the error rates of these small sensors are higher than those of the larger, more expensive sensors used by law enforcement, for example, because they scan a smaller portion of the finger and retain a lower-resolution image.
Facial recognition is gaining popularity as a security measure for laptops and mobile phones, among other things because it can be implemented using the cameras that are usually built into these devices. Systems based on facial recognition are quite accurate if the photos are taken under controlled conditions - for example, if the person is photographed in room lighting, facing forward and wearing a normal facial expression. However, the systems fail if the original image and the new image differ in face orientation, lighting conditions, facial expressions, age, or the addition of glasses or a beard. This sensitivity to changes in the routine is especially problematic in video surveillance systems, where the subjects are not standing in front of the camera in a predetermined position. It is possible that in the next decade the technology will advance enough to allow mechanized, complete and real-time facial recognition in video surveillance systems.
Identification using the iris is very fast and accurate because the complex pattern of the iris is probably unique to each person and does not change over the years. The person looks into the scanner for a few seconds, and the iris pattern is captured, analyzed and recorded. The identification is done by comparing the recorded data with those found in a database. Due to the method's speed and accuracy, iris-based identification systems have recently been developed on a large scale, such as that of British immigration control. Passengers registered in the database can bypass the long lines of border control at the airport and thus shorten the waiting time.
However, iris detection also has its drawbacks. The method is based, among other things, on the use of algorithms, which represent the random pattern of the iris through a sequence of bits. A human expert is unable to determine if two iris patterns are indeed identical, therefore iris data is not admissible as evidence in a court of law.
Imperfect matches
The developers of the biometric identification systems face additional difficulties. Unlike identification systems based on a password or some object, biometric systems have to make decisions based on imperfect matches. Any system that makes comparisons may create two basic types of errors: in the case of "incorrect confirmation" the system mistakenly determines that there is a match between the received template and the template in the database, and in the case of "wrong rejection" the system mistakenly determines that there is no match between the received template and the template in the database.
Most experts agree that the false approval and false rejection rates of a biometric identification system should be less than 0.1% (ie, one error per 1,000 match determinations and one error per 1,000 mismatch determinations). But in tests by the American Standards Institute from 2003 to 2006, it became clear that the error rates of identification systems based on fingerprints, face, iris and voice - another characteristic of biometric identification systems - were all greater than 0.1%.
Increasing the matching threshold can decrease the false approval rates, but this will result in increasing the false rejection rates. In order to reduce the rates of both types of errors at the same time, biometric sensors must be developed that will produce higher quality images and improve the characteristics extraction and comparison capabilities. The system designers will also have to ensure that the systems are protected against tampering: we would expect that it would not be possible to eavesdrop on biometric information and re-enter the system, or change the biometric hardware or software. Such tampering attempts are typical of all identification systems, even those based on a password or an object, so it is possible to deal with them using the tools accepted in the field. For example, encryption methods can be used to prevent hackers from accessing, using, or modifying information.
A much bigger challenge is designing a secure biometric identification system, which will confirm only the real owner of the characteristics and will not be misled by imitations, such as a plastic copy of a finger. For this purpose, you can use sensors that detect heat or other signs of life, and ensure that the input source is not an inanimate object.
Perhaps the most effective approach to improving the accuracy, reliability and security of biometric systems is to use a combination of several biometric characteristics or several appearances of the same characteristic (eg, more than one fingerprint). Strengthening a person's identification through such combinations makes it possible to prove that the biometric data does indeed belong to its real owner and not to an impostor, and it is more difficult to disprove this proof. Many passport recognition systems are being developed according to this approach. The US-VISIT program, which previously only scanned two fingers of visitors who are not citizens of the United States, has begun scanning all ten fingers, and has future capability to include facial recognition as well.
The question of privacy
The use of biometrics raises concerns about the issue of privacy. Who is the owner of the information - the person or the service providers? Will they use the information for purposes it was not intended for, for example to learn from it about the state of the person's health? The future biometric systems will certainly operate in moderation, and they will record the user's biometric characteristics without his active involvement. Such a course of action further exacerbates the problems associated with the issue of privacy.
At the moment we do not see any real and practical solutions for these various problems on the horizon. However, we believe that it will be possible to solve them through public discussion and policy formulation. There is no other way. It is only a matter of time until further improvements in biometric tools bring them to the fore in efforts to combat the common problems of security and identity fraud that society faces.
Anil K. Jain is a professor in the Department of Computer Science at Michigan State University, who has written several books on biometrics. Shaarat Pankanti is the director of the computer vision group at IBM's research center in Yorktown Heights, New York. He is now engaged in the development of multi-purpose object recognition systems. Jain and Penkanti have many patents on fingerprints. The full article was published in the December issue of "Scientific American"
The biometric is already here
- The European Union: EU countries are obliged to start issuing passports that incorporate biometric information by the summer of 2009.
- UK: Some school cafeterias have introduced payment systems based on fingerprint recognition instead of using cash.
- United States: The payroll manager of the City of New York signed a contract worth 181.1 million dollars with the company "Science International Applications" from San Diego for the installation of a biometric attendance clock that scans hands and fingers.

10 תגובות
A serious violation of individual rights! And in democracy!
We must not agree to that.
What is fingerprint information worth if today there are ways to steal such information and create an exact copy of the fingerprint from a special rubber polymer.
It will be possible to incriminate people in this way for various and different acts for doing no wrong in their hands.
It's happening right now!!!!
Every job seeker at the employment bureau signs with a fingerprint
In other words, every unemployed person is a potential criminal...
Maybe you can't fake a fingerprint, but who has the data
Can associate a particular fingerprint with someone else's personal details
and drop a "bag" on him that they won't know where it came from
Think about it, 1984 is long gone, and technology is starting to stifle more than ever...
point:
I didn't notice the context in which the question was asked.
The objective meaning remains as it was but even identical twins differ in some characteristics (like fingerprints).
The problem becomes a purely technical problem, but it is better not to create such a problem and come to Zion Goel.
If someone knows how to duplicate one for one, he probably also knows how to engineer small differences
Surely the question has an objective meaning.
On the other hand, it is quite trivial - this is more or less the case with identical twins. It is true that in this case the double was created in the womb, but what is the difference?
There is no doubt that these are different people.
Suppose a certain person is engineered to be a duplicate of another person.
How then is it determined who is who? And does this question have any objective meaning at all (apart from the network structure in the brain)?
This body is my body, and this life is my life. crossing every border.
Tomorrow the government can decide that everyone should cut off the middle nail of the finger and keep it in the database, so that there is an original DNA sample. Even then a decision will be made and people like idiots will do and agree.
This thing violates the most basic right of individual freedom.
Why would I, as a citizen in a liberal and democratic country, agree to a proposal that was not accepted by the majority of the people to transfer personal data, the shape of my eyes, my fingers, etc. to the government and law enforcement. Infringes on personal freedom and individual modesty.
It is forbidden under any circumstances to approve such a thing.
"The Biometric Database Law and Yair Lapid" to which I refer in this article
http://webster.co.il/2009/03/30/1044/